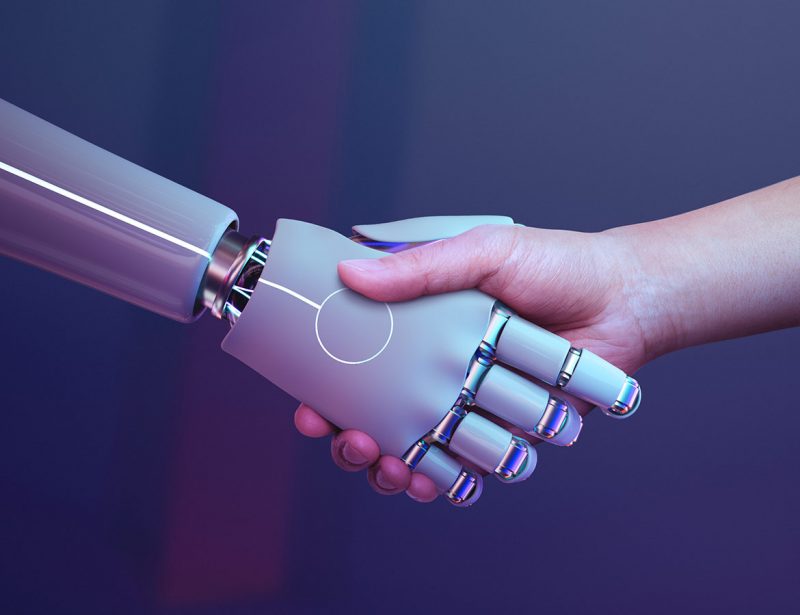
Advanced Cyber Protection
Our cutting-edge cybersecurity solutions safeguard your digital assets against evolving threats. From threat detection to proactive defense strategies, we ensure comprehensive security tailored to your needs.
Threat Detection & Response
Stay ahead of cyber threats with our intelligent detection and rapid response solutions. We analyze, monitor, and neutralize potential risks in real time to keep your business secure and resilient.
24/7 Security Support
Our dedicated cybersecurity experts are available around the clock to provide assistance, threat mitigation, and system optimization. We ensure continuous protection with proactive monitoring and rapid response.
Who we are
We provide cutting-edge cybersecurity solutions, ensuring robust protection for businesses with advanced threat detection, risk management, and 24/7 expert support.
10+
Years of Experience
70K+
Satisfied Custommers
50+
Successfull Projects
PENETRATION TESTS
PENETRATION TESTS
PENETRATION TESTS
PENETRATION TESTS
PENETRATION TESTS
PENETRATION TESTS
PENETRATION TESTS
PENETRATION TESTS
care features
Provide Awesome Service With Our Tools
Network Penetration Testing
Identify vulnerabilities in your network infrastructure, including firewalls, routers, and switches.
Web Application Penetration Testing
Test your web applications for security flaws like SQL injection, XSS, and CSRF vulnerabilities.
Mobile Application Penetration Testing
Assess the security of your mobile apps, including data storage, authentication, and API vulnerabilities.
Cloud Infrastructure Penetration Testing
Evaluate the security of your cloud environments, including misconfigurations and access control issues.
Wireless Network Penetration Testing
Detect weaknesses in your wireless networks, such as weak encryption or unauthorized access points.
Social Engineering Penetration Testing
Simulate real-world phishing, baiting, and pretexting attacks to test employee awareness.

Physical Penetration Testing
Assess the security of physical access controls, such as doors, locks, and surveillance systems.
API Penetration Testing
Identify vulnerabilities in your APIs, including authentication flaws and data exposure risks.
IoT Device Penetration Testing
Test the security of IoT devices, including firmware vulnerabilities and insecure communication protocols.
Red Team vs. Blue Team Exercises
Simulate advanced cyber attacks (Red Team) and test your defense mechanisms (Blue Team) in real-time.
Compliance-Based Penetration Testing
Ensure your systems meet industry standards like GDPR, PCI-DSS, and ISO 27001 through targeted testing.
Post-Exploitation Analysis
Analyze the impact of successful attacks and provide actionable recommendations to mitigate risks.
FEATURED WORKS
FEATURED WORKS
FEATURED WORKS
FEATURED WORKS
FEATURED WORKS
FEATURED WORKS
FEATURED WORKS
FEATURED WORKS
Who we are
What People Say
"Their penetration testing services are thorough and reliable. They secured our networks, apps, and cloud systems effortlessly."

Joe Marvin
COMPANY SEO
"Their expertise in cybersecurity is unmatched. They identified vulnerabilities we didn’t even know existed and fixed them promptly."

Kate Johnson
COMPANY SEO
"Their compliance-based testing ensured we met all industry standards. Now, we can focus on growth without worrying about security."

Joe Marvin
COMPANY SEO